Universal 2nd Factor (U2F) is an open standard that strengthens and simplifies two-factor authentication (2FA) using specialized Universal Serial Bus (USB) or near-field communication (NFC) devices based on similar security technology found in smart cards.[1][2][3][4][5] It is succeeded by the FIDO2 Project, which includes the W3C Web Authentication (WebAuthn) standard and the FIDO Alliance's Client to Authenticator Protocol 2 (CTAP2).[6]
While initially developed by Google and Yubico, with contribution from NXP Semiconductors, the standard is now hosted by the FIDO Alliance.[7][8]
Advantages and disadvantages
While time-based one-time passwords (e.g. 6-digit codes generated on Google Authenticator) were a significant improvement over SMS-based security codes, a number of security vulnerabilities were still possible to exploit, which U2F sought to improve. Specifically:
| Issue | TOTP | U2F |
|---|---|---|
| Shared secret |
|
|
| Man-in-the-middle attack |
|
|
| Convenience / eavesdropping |
|
|
In terms of disadvantages, one significant difference and potential drawback to be considered regarding hardware-based U2F solutions is that unlike with TOTP shared-secret methods, there is no possibility of "backing up" recovery codes or shared secrets. If a hardware duplicate or alternative hardware key is not kept and the original U2F hardware key is lost, no recovery of the key is possible (because the private key exists only in hardware). Therefore, for services that do not provide any alternative account recovery method, the use of U2F should be carefully considered.
Design
The USB devices communicate with the host computer using the human interface device (HID) protocol, essentially mimicking a keyboard.[9] This avoids the need for the user to install special hardware driver software in the host computer and permits application software (such as a browser) to directly access the security features of the device without user effort other than possessing and inserting the device. Once communication is established, the application exercises a challenge–response authentication with the device using public-key cryptography methods and a secret unique device key manufactured into the device.[10]
Vulnerabilities
The device key is vulnerable to malicious manufacturer duplication.
In 2020, independent security researchers found a method to extract private keys from Google Titan Key, a popular U2F hardware security token.[11][12][13] The method required physical access to the key for several hours, several thousand euros-worth of equipment, and was destructive to the plastic case of the key.[11][12][13] The attackers concluded that the difficulty of the attack meant that people were still safer to use the keys than not.[11][12][13] The attack was possible due to a vulnerability in the A700X microchip made by NXP Semiconductors, which is also used in security tokens made by Feitian and Yubico, meaning that those tokens are also vulnerable.[11][14] The vulnerability was responsibly disclosed to the affected manufacturers so that it might be fixed in future products.[11][12][13]
Support and use
U2F security keys are supported by Google Chrome since version 38,[2] Firefox since version 57[15] and Opera since version 40. U2F security keys can be used as an additional method of two-step verification on online services that support the U2F protocol, including Google,[2] Azure,[16] Dropbox,[17] GitHub,[18] GitLab,[19] Bitbucket,[20] Nextcloud,[21] Facebook,[22] and others.[23]
Chrome, Firefox, and Opera were, as of 2015, the only browsers supporting U2F natively. Microsoft has enabled FIDO 2.0 support for Windows 10's Windows Hello login platform.[24] Microsoft Edge[25] browser gained support for U2F in the October 2018 Windows Update. Microsoft accounts, including Office 365, OneDrive, and other Microsoft services, do not yet have U2F support. Mozilla has integrated it into Firefox 57, and enabled it by default in Firefox 60[26][27][28][29] and Thunderbird 60.[30] Microsoft Edge starting from build 17723 support FIDO2.[31] As of iOS and iPadOS 13.3 Apple now supports U2F in the Safari browser on those platforms.
Specifications
The U2F standard has undergone two major revisions:
Additional specification documents may be obtained from the FIDO web site.[34]
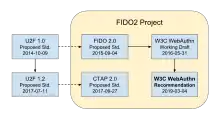
The U2F 1.0 Proposed Standard (October 9, 2014) was the starting point for a short-lived specification known as the FIDO 2.0 Proposed Standard (September 4, 2015). The latter was formally submitted to the World Wide Web Consortium (W3C) on November 12, 2015.[35] Subsequently, the first Working Draft of the W3C Web Authentication (WebAuthn) standard was published on May 31, 2016. The WebAuthn standard has been revised numerous times since then, becoming a W3C Recommendation on March 4, 2019.
Meanwhile the U2F 1.2 Proposed Standard (April 11, 2017) became the starting point for the Client to Authenticator Protocol (CTAP) Proposed Standard, which was published on September 27, 2017. FIDO CTAP complements W3C WebAuthn, both of which are in scope for the FIDO2 Project.
WebAuthn and CTAP provide a complete replacement for U2F, which has been renamed "CTAP1" in the latest version of the FIDO2 standard.[36] The WebAuthn protocol is backward-compatible (via the AppID extension) with U2F-only security keys[37] but the U2F protocol is not compatible with a WebAuthn-only authenticator.[38][39][36] Some authenticators support both U2F and WebAuthn while some WebAuthn clients support keys created via the legacy U2F API.
References
- ↑ Turner, Adam (November 5, 2014). "Google security keys may offer extra layer of online protection". The Sydney Morning Herald. Fairfax Media. Retrieved November 28, 2014.
- 1 2 3 "What browsers support U2F?". Yubico. Archived from the original on August 18, 2017. Retrieved August 17, 2017.
- ↑ Bradley, Tony (October 21, 2014). "How a USB key drive could remove the hassles from two-factor authentication". PCWorld. IDG Consumer & SMB. Retrieved November 28, 2014.
- ↑ "FIDO Universal 2nd Factor". Yubico AB. Retrieved November 28, 2014.
- ↑ Diallo, Amadou (November 30, 2013). "Google Wants To Make Your Passwords Obsolete". Forbes. Retrieved November 28, 2014.
- ↑ Octopus, Cipher. "An In-Depth Guide to FIDO Protocols: U2F, UAF, and WebAuthn (FIDO2)". blog.strongkey.com. Retrieved 9 March 2021.
- ↑ "FIDO Alliance – download specifications". FIDO Alliance. Retrieved October 19, 2017.
- ↑ Krebs, Brian (October 14, 2014). "Google Accounts Now Support Security Keys". Krebs on Security. Retrieved November 28, 2014.
- ↑ "FIDO U2F HID Protocol Specification". FIDO Alliance. October 9, 2014. Retrieved July 24, 2018.
- ↑ "Key generation". Yubico. Retrieved 31 July 2018.
- 1 2 3 4 5 "Hackers can clone Google Titan 2FA keys using a side channel in NXP chips". Ars Technica. 2021-01-08. Retrieved 2021-01-13.
- 1 2 3 4 Cimpanu, Catalin (2021-01-08). "New side-channel attack can recover encryption keys from Google Titan security keys". ZDNet. Retrieved 2021-01-13.
- 1 2 3 4 "Researchers Show Google's Titan Security Keys Can Be Cloned". SecurityWeek. 2021-01-11. Retrieved 2021-01-13.
- ↑ Ducklin, Paul (2021-01-11). "Google Titan security keys hacked by French researchers". Naked Security. Retrieved 2021-01-13.
- ↑ J.C. Jones (April 4, 2019). "Backward-Compatibility FIDO U2F support shipping soon in Firefox". Mozilla Security Blog.
- ↑ "Passwordless authentication options for Azure Active Directory". Retrieved 14 April 2021.
- ↑ Heim, Patrick; Patel, Jay (August 12, 2015). "Introducing U2F support for secure authentication". Dropbox Blog. Retrieved August 12, 2015.
- ↑ Olsen, Risk (October 1, 2015). "GitHub supports Universal 2nd Factor authentication". github.com/blog. GitHub. Retrieved October 1, 2015.
- ↑ Nwaigwe, Amara (June 22, 2016). "Support for Universal 2nd Factor Authentication". GitLab Blog. Retrieved July 9, 2016.
- ↑ Kells, TJ (June 22, 2016). "Universal 2nd Factor (U2F) now supported in Bitbucket Cloud". Bitbucket Blog. Retrieved June 22, 2016.
- ↑ "Nextcloud 11 sets new standard for security and scalability". Nextcloud. Retrieved 23 December 2016.
- ↑ "Security Key for safer logins with a touch". Facebook. Retrieved 27 January 2017.
- ↑ "USB-Dongle Authentication". Josh Davis. Retrieved 23 January 2023.
- ↑ Ingalls, Dustin (February 13, 2015). "Microsoft Announces FIDO Support Coming to Windows 10". Windows Blog. Retrieved October 3, 2015.
- ↑ "Microsoft Edge now supports passwordless sign-ins". Engadget. Retrieved 2018-10-04.
- ↑ "Firefox 57 has native support for U2F". Mozilla. Retrieved November 1, 2017.
- ↑ "U2F Support Addon". Retrieved May 8, 2016.
- ↑ "Firefox Nightly enables support for FIDO U2F Security Keys". Yubico blog. 2017-09-22. Retrieved September 27, 2017.
- ↑ "Firefox 60.0 release notes". Retrieved May 11, 2018.
- ↑ "Thunderbird 60.0 release notes". Retrieved June 22, 2018.
- ↑ "Introducing Web Authentication in Microsoft Edge — Microsoft Edge Dev BlogMicrosoft Edge Dev Blog". blogs.windows.com. 2018-07-30. Retrieved 2018-08-03.
- ↑ "FIDO U2F V1.0 Proposed Standard 2014-10-09". FIDO Alliance. 9 October 2014. Retrieved 3 May 2019.
- ↑ "FIDO U2F V1.2 Proposed Standard 2017-04-11". FIDO Alliance. 11 April 2017. Retrieved 3 May 2019.
- ↑ "Download Specifications". FIDO Alliance. Retrieved 13 February 2019.
- ↑ "Submission Request to W3C: FIDO 2.0 Platform Specifications 1.0". World Wide Web Consortium (W3C). Retrieved 12 February 2019.
- 1 2 Chong, Jerrod (1 August 2018). "10 Things You've Been Wondering About FIDO2, WebAuthn, and a Passwordless World". Retrieved 1 May 2019.
- ↑ Balfanz, Dirk; Czeskis, Alexei; Hodges, Jeff; Jones, J.C.; Jones, Michael B.; Kumar, Akshay; Liao, Angelo; Lindemann, Rolf; Lundberg, Emil (eds.). "Web Authentication: An API for accessing Public Key Credentials Level 1 (latest)". World Wide Web Consortium (W3C). Retrieved 4 March 2019.
- ↑ Hakamine, Frederico (22 January 2019). "Understanding FIDO Standards: Your Go-To Guide". Retrieved 22 July 2021.
- ↑ Salam, Feroz (25 August 2018). "Why you can't use Firefox to register a U2F key with Google". Retrieved 1 May 2019.