| Computer network types by scale |
|---|
 |

A wireless LAN (WLAN) is a wireless computer network that links two or more devices using wireless communication to form a local area network (LAN) within a limited area such as a home, school, computer laboratory, campus, or office building. This gives users the ability to move around within the area and remain connected to the network. Through a gateway, a WLAN can also provide a connection to the wider Internet.
Wireless LANs based on the IEEE 802.11 standards are the most widely used computer networks in the world. These are commonly called Wi-Fi, which is a trademark belonging to the Wi-Fi Alliance. They are used for home and small office networks that link together laptop computers, printers, smartphones, Web TVs and gaming devices with a wireless router, which links them to the internet. Hotspots provided by routers at restaurants, coffee shops, hotels, libraries, and airports allow consumers to access the internet with portable wireless devices.
History
Norman Abramson, a professor at the University of Hawaii, developed the world's first wireless computer communication network, ALOHAnet. The system became operational in 1971 and included seven computers deployed over four islands to communicate with the central computer on the Oahu island without using phone lines.[1]

Wireless LAN hardware initially cost so much that it was only used as an alternative to cabled LAN in places where cabling was difficult or impossible. Early development included industry-specific solutions and proprietary protocols, but at the end of the 1990s these were replaced by technical standards, primarily the various versions of IEEE 802.11 (in products using the Wi-Fi brand name).
Beginning in 1991, a European alternative known as HiperLAN/1 was pursued by the European Telecommunications Standards Institute (ETSI) with a first version approved in 1996. This was followed by a HiperLAN/2 functional specification with ATM influences accomplished February 2000. Neither European standard achieved the commercial success of 802.11, although much of the work on HiperLAN/2 has survived in the physical specification (PHY) for IEEE 802.11a, which is nearly identical to the PHY of HiperLAN/2.
In 2009 802.11n was added to 802.11. It operates in both the 2.4 GHz and 5 GHz bands at a maximum data transfer rate of 600 Mbit/s. Most newer routers are dual-band and able to utilize both wireless bands. This allows data communications to avoid the crowded 2.4 GHz band, which is also shared with Bluetooth devices and microwave ovens. The 5 GHz band also has more channels than the 2.4 GHz band, permitting a greater number of devices to share the space. Not all WLAN channels are available in all regions.
A HomeRF group formed in 1997 to promote a technology aimed at residential use, but it disbanded in January 2003.[2]
Architecture
Stations
All components that can connect into a wireless medium in a network are referred to as stations. All stations are equipped with wireless network interface controllers. Wireless stations fall into two categories: wireless access points (WAPs) and clients. WAPs are base stations for the wireless network. They transmit and receive radio frequencies for wireless-enabled devices to communicate with. Wireless clients can be mobile devices such as laptops, personal digital assistants, VoIP phones and other smartphones, or non-portable devices such as desktop computers, printers, and workstations that are equipped with a wireless network interface.
Service set
The basic service set (BSS) is a set of all stations that can communicate with each other at PHY layer. Every BSS has an identification (ID) called the BSSID, which is the MAC address of the access point servicing the BSS.
There are two types of BSS: Independent BSS (also referred to as IBSS), and infrastructure BSS. An independent BSS (IBSS) is an ad hoc network that contains no access points, which means they cannot connect to any other basic service set. In an IBSS the STAs are configured in ad hoc (peer-to-peer) mode.
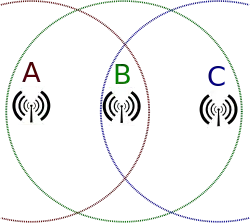
An extended service set (ESS) is a set of connected BSSs. Access points in an ESS are connected by a distribution system. Each ESS has an ID called the SSID which is a 32-byte (maximum) character string.
A distribution system (DS) connects access points in an extended service set. The concept of a DS can be used to increase network coverage through roaming between cells. DS can be wired or wireless. Current wireless distribution systems are mostly based on WDS or Mesh protocols,[3] though other systems are in use.
Types of wireless LANs
The IEEE 802.11 has two basic modes of operation: infrastructure and ad hoc mode. In ad hoc mode, mobile units communicate directly peer-to-peer. In infrastructure mode, mobile units communicate through a wireless access point (WAP) that also serves as a bridge to other networks such as a local area network or the Internet.
Since wireless communication uses a more open medium for communication in comparison to wired LANs, the 802.11 designers also included encryption mechanisms: Wired Equivalent Privacy (WEP), no longer considered secure, Wi-Fi Protected Access (WPA, WPA2, WPA3), to secure wireless computer networks. Many access points will also offer Wi-Fi Protected Setup, a quick, but no longer considered secure, method of joining a new device to an encrypted network.
Infrastructure
Most Wi-Fi networks are deployed in infrastructure mode. In infrastructure mode, wireless clients, such as laptops and smartphones, connect to the WAP to join the network. The WAP usually has a wired network connection and may have permanent wireless connections to other WAPs.
WAPs are usually fixed and provide service to their client nodes within range. Some networks will have multiple WAPs using the same SSID and security arrangement. In that case, connecting to any WAP on that network joins the client to the network, and the client software will try to choose the WAP that gives the best service, such as the WAP with the strongest signal.
Peer-to-peer

An ad hoc network is a network where stations communicate only peer-to-peer (P2P). There is no base and no one gives permission to talk. This is accomplished using the Independent Basic Service Set (IBSS). A Wi-Fi Direct network is a different type of wireless network where stations communicate peer-to-peer.[4] In a peer-to-peer network wireless devices within range of each other can discover and communicate directly without involving central access points.
In a Wi-Fi P2P group, the group owner operates as an access point and all other devices are clients. There are two main methods to establish a group owner in the Wi-Fi Direct group. In one approach, the user sets up a P2P group owner manually. This method is also known as autonomous group owner (autonomous GO). In the second method, called negotiation-based group creation, two devices compete based on the group owner intent value. The device with higher intent value becomes a group owner and the second device becomes a client. Group owner intent value can depend on whether the wireless device performs a cross-connection between an infrastructure WLAN service and a P2P group, available power in the wireless device, whether the wireless device is already a group owner in another group or a received signal strength of the first wireless device.
IEEE 802.11 defines the PHY and medium access control (MAC) layers based on carrier-sense multiple access with collision avoidance (CSMA/CA). This is in contrast to Ethernet which uses carrier-sense multiple access with collision detection (CSMA/CD). The 802.11 specification includes provisions designed to minimize collisions because mobile units have to contend with the hidden node problem where two mobile units may both be in range of a common access point, but out of range of each other.
Bridge
A bridge can be used to connect networks, typically of different types. A wireless Ethernet bridge allows the connection of devices on a wired Ethernet network to a wireless network. The bridge acts as the connection point to the wireless LAN.
Wireless distribution system
A wireless distribution system (WDS) enables the wireless interconnection of access points in an IEEE 802.11 network. It allows a wireless network to be expanded using multiple access points without the need for a wired backbone to link them, as is traditionally required. The notable advantage of a WDS over some other solutions is that it preserves the MAC addresses of client packets across links between access points.[5]
An access point can be either a main, relay, or remote base station. A main base station is typically connected to the wired Ethernet. A relay base station relays data between remote base stations, wireless clients or other relay stations to either a main or another relay base station. A remote base station accepts connections from wireless clients and passes them to relay or main stations.
Because data is forwarded wirelessly, consuming wireless bandwidth, throughput in this method is halved for wireless clients not connected to a main base station. Connections between base stations are done at layer-2 and do not involve or require layer-3 IP addresses. WDS capability may also be referred to as repeater mode because it appears to bridge and accept wireless clients at the same time (unlike traditional bridging).
All base stations in a WDS must be configured to use the same radio channel and share WEP keys or WPA keys if they are used. They can be configured to different service set identifiers. WDS also requires that every base station be configured to forward to others in the system as mentioned above.
Roaming

There are two definitions for wireless LAN roaming:
- Internal roaming: The mobile station (MS) moves from one access point (AP) to another AP within a home network if the signal strength is too weak. An authentication server performs the re-authentication of MS via 802.1x (e.g. with PEAP). The billing of QoS is in the home network. A MS roaming from one access point to another often interrupts the flow of data between the MS and an application connected to the network. The MS, for instance, periodically monitors the presence of alternative APs (ones that will provide a better connection). At some point, based on proprietary mechanisms, the MS decides to re-associate with an AP having a stronger wireless signal. The MS, however, may lose a connection with an AP before associating with another access point. To provide reliable connections with applications, the MS must generally include software that provides session persistence.[6]
- External roaming: The MS (client) moves into a WLAN of another wireless Internet service provider (WISP) and takes their services. The user can use a foreign network independently from their home network, provided that the foreign network allows visiting users on their network. There must be special authentication and billing systems for mobile services in a foreign network.
See also
References
- ↑ "History of Wireless". Johns Hopkins Bloomberg School of Public Health. Archived from the original on 2007-02-10. Retrieved 2007-02-17.
- ↑ Wayne Caswell (November 17, 2010). "HomeRF Archives". Archived from the original on May 29, 2018. Retrieved July 16, 2011.
- ↑ Wireless Mesh Routing Compared WDS, archived from the original on 2023-01-17, retrieved 2022-11-11
- ↑ "Is this the same as Ad Hoc mode?". Archived from the original on 2013-08-30.
- ↑ "Wireless Distribution System Linked Router Network". DD-WRT Wiki. Archived from the original on June 30, 2017. Retrieved December 31, 2006.
- ↑ "How Wi-Fi Roaming Really Works". Archived from the original on 2019-02-23. Retrieved 2008-10-09.